
The life of a cybersecurity executive has been upended by the arrival of a new class of artificial intelligence systems that can sift through vast swathes of software and surface weaknesses at a speed no human team can match.
Sharda Tickoo, country manager for India & SAARC at TrendAI (formerly Trend Micro), says she has spent the past fortnight incessantly talking to clients, partners and stakeholders — fielding alarm, explaining context, and mapping out a path forward. “It is now established that AI has crossed a threshold where it can discover vulnerabilities at a level comparable with top human researchers, but at a speed and scale humans simply cannot match,” she says.
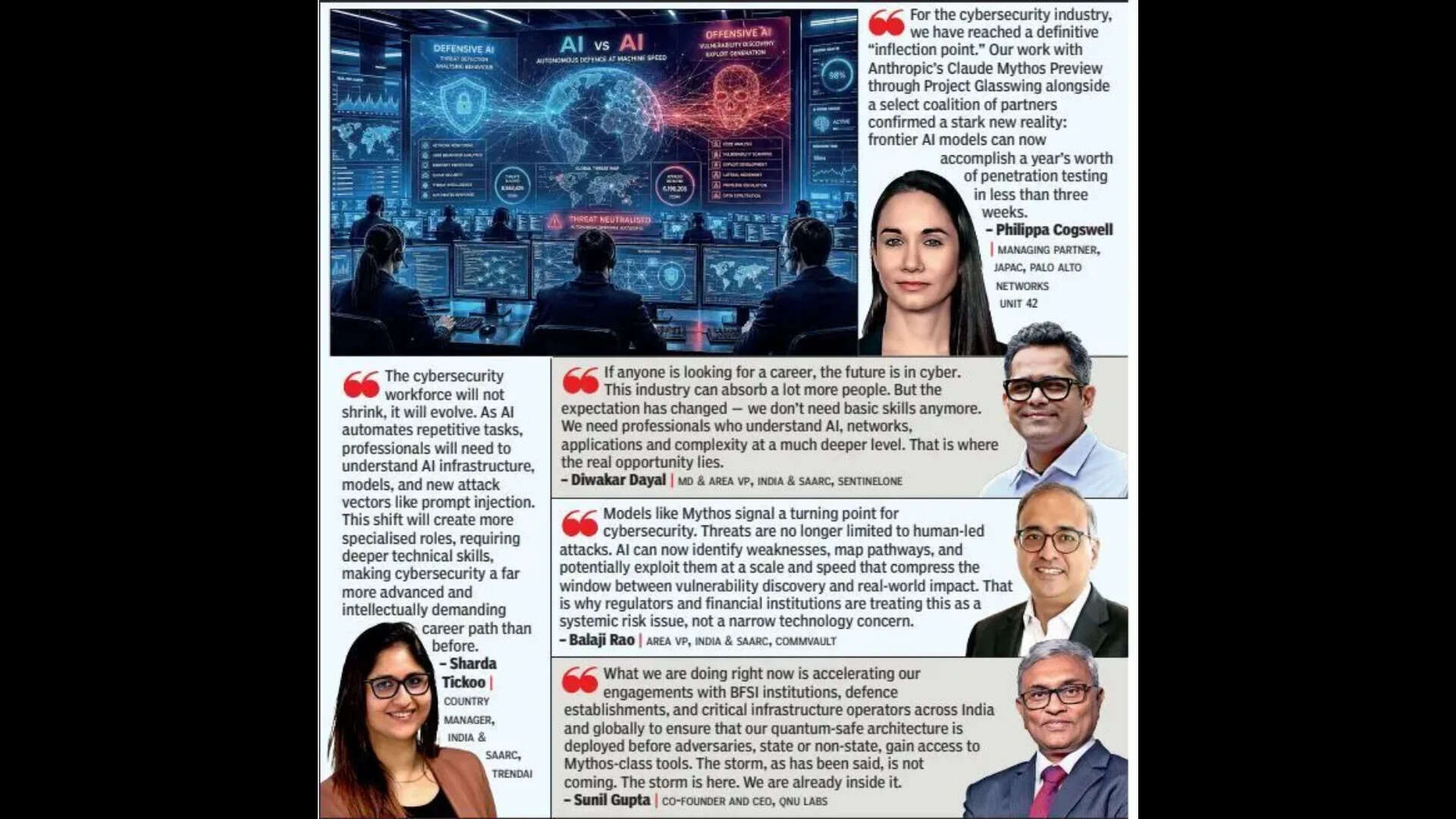
“The same capability can defend or be weaponised.”The catalyst for this collective anxiety is Mythos, a frontier AI model developed by Anthropic that has demonstrated a remarkable — and deeply unsettling — ability to surface zero-day vulnerabilities across major operating systems and web browsers. Its emergence has prompted crisis talks among regulators worldwide, and inside the industry, it has accelerated a reckoning that many say was long overdue.
Diwakar Dayal, MD and area VP for India & SAARC at SentinelOne, has lived through every major technology wave of the past three decades — the birth of the internet, the cloud era, the mobile revolution. He is unequivocal that this one is different. “Every previous wave took years to unfold. This one is almost on steroids,” he says. “Unless you respond to AI-driven attacks with AI-driven defence, it is an impossible battle.
” For Dayal, the starkest illustration of the shift is the shrinking gap between vulnerability discovery and exploitation. “Fifteen years back, the gap was maybe two years. Then it became months. Now it is hours,” he says. “You cannot patch everything. That game is already lost.”That compression has rendered traditional security practices inadequate at a structural level. For years, the industry’s backbone was the patch cycle — find the flaw, fix the flaw.
But as Tickoo notes, the backlog of unpatched vulnerabilities was already enormous before Mythos arrived. “Enterprises are still struggling to patch n-minus-ten vulnerabilities (security flaws present in software versions that are ten releases behind the current, most up-to-date version),” she says.
“Mythos has not created new vulnerabilities so much as revealed what was already there. It simply compresses the timeline of exploitation.”
AI native defenceThe industry’s response is coalescing around a single principle: security must become AI-native, not merely AI-assisted. Tickoo is emphatic on the distinction. “Traditional tools were built for human-led detection. That model does not hold when AI can uncover thousands of vulnerabilities across systems,” she says. At TrendAI, that means integrating Claude models directly into its platform to drive what she calls “agentic autonomous security operations” — systems that learn continuously, prioritise intelligently, and act without waiting for human instruction.
The company’s Zero Day Initiative programme, long a researcher-driven effort to surface vulnerabilities, is itself being made more automatic and agentic. Dayal echoes this at SentinelOne, where the company’s endpoint security platform operates in real time, detecting and containing threats at machine speed irrespective of whether a patch exists. “If you use traditional methods,” he says simply, “it is not possible.”For the time being practices like virtual patching — placing a protective wrapper around a known vulnerability to block exploitation without requiring a restart or downtime — have become a critical stopgap in this environment. Tickoo explains that while it has always existed, it is now becoming non-negotiable. “You will not be able to patch everything because it requires downtime,” she says. “Virtual patching acts as a compensating control.
Technically, the vulnerability is still there inside the asset, but the moment anyone tries to exploit it, it will be blocked.”Satykam Acharya, co-founder and director of offensive practices at Infopercept, argues that the real challenge is not simply discovery but prioritisation. “Most breaches are not caused by complex zero-days,” he says. “They come from misconfigurations, weak identity controls, or exposed credentials.
In many cases, attackers are no longer hacking in — they are simply logging in.” His firm’s approach focuses on helping clients answer three questions: which vulnerabilities are actually exploitable, which create real business risk, and what to fix first.Philippa Cogswell, managing partner for JAPAC at Palo Alto Networks Unit 42, describes the present moment as a “definitive inflection point”, noting that Palo Alto’s own tests with Mythos showed how the AI system completed a year’s worth of penetration testing in under three weeks.
“Defending against an attacker who can do in minutes what a team does in weeks requires a completely different approach,” she says. “This is why we are seeing a move towards platformisation, where security data is consolidated so AI can detect, prioritise and respond to threats in real time.
”Balaji Rao, Area VP for India & SAARC at Commvault, says detection and prevention remain essential, but they are no longer enough when attack chains can move at machine speed.
He says that Commvault, which specialises in data protection and cyber recovery for enterprises, has adopted a “ResOps” approach, where recovery systems are continuously validated rather than periodically reviewed.Sunil Gupta, co-founder and CEO of QNu Labs, takes the most unsparing view: “Mythos is not a warning. It is a verdict on the past decade of cybersecurity complacency.” He advocates for quantum-safe architectures as the only route beyond what he calls “a continuous, expensive, losing cycle” of patching.Job opportunities galoreFor all the turbulence, there is one note of striking optimism: this is, by most accounts, an extraordinary moment to build a career in cybersecurity. “If anyone is looking for a career, the future is in cyber,” says Dayal. “This industry can absorb a lot more people.” But the bar has risen sharply. The next generation of professionals will need fluency not just in networks and systems, but in AI infrastructure, model security, prompt injection attacks, and the architecture of agentic systems.
“We don’t need people with basic knowledge anymore,” Dayal says. “We need people who can understand complexity at a much deeper level.” Tickoo agrees: “It will become more specialised — and there will be a reskilling from a cybersecurity standpoint.”

